Your photos security
As more and more photographers are adopting virtual (online) photo shoots with the Shutter Studio, the question on security and privacy is raised more frequently.
This is a completely reasonable question! We, as humans, want others to respect our privacy. A photoshoot can be a very intimate experience that relies on trust. We will not allow a complete stranger to take photos of ourselves, we do not want to express our true self to a person we barely know.

We at Shutter Studio are in love with photography, we have been doing it for many years already and not going to stop anytime soon! That’s why we understand all such privacy concerns from our own experience and are committed to provide the best service possible, so that photographers and their clients can be ultimately confident that the only thing they need to think about is how to have as much fun during the process as possible!
Let us explain in more detail, what we have done so far and what our nearest plans are to make sure that all photos taken with Shutter Studio are truly safe and secure.
First of all, let’s discuss the key components of our service:
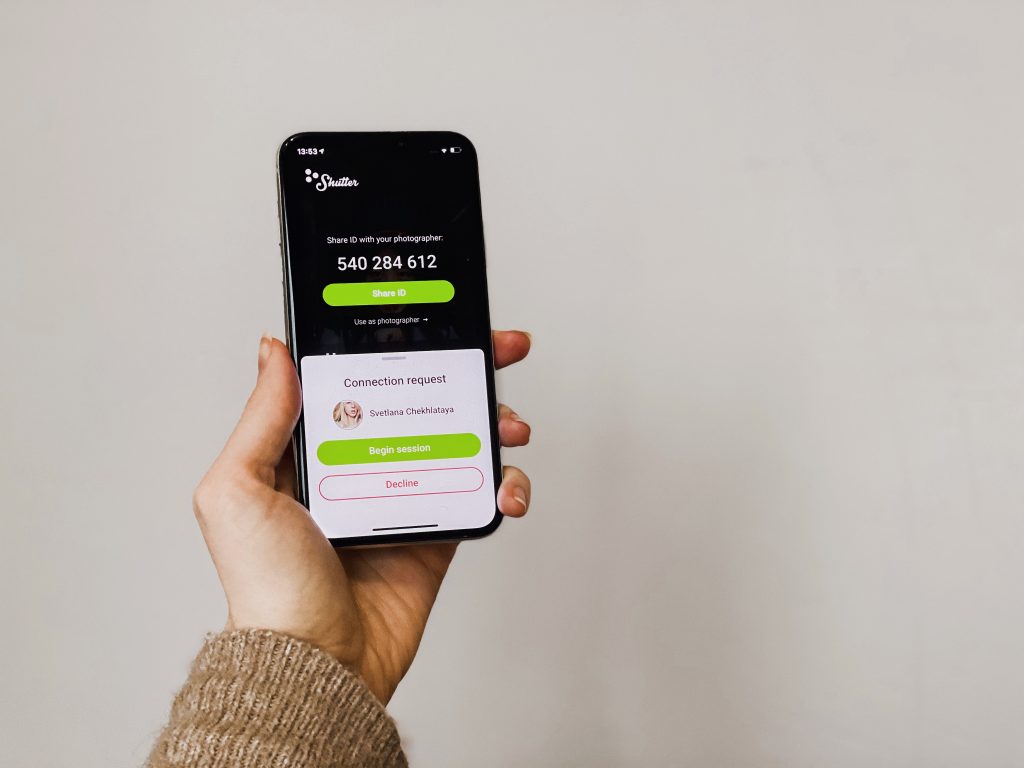
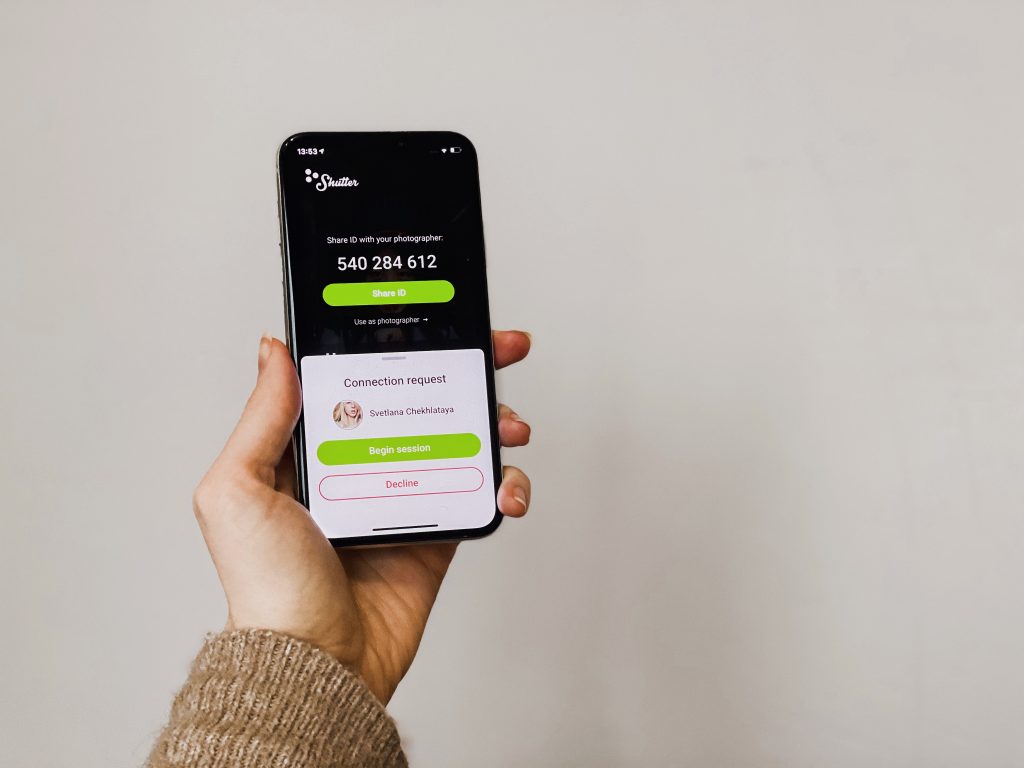
- A model installs Shutter App application on his or her mobile phone, which generates a unique number to identify this phone inside Shutter Studio ecosystem
- A photographer uses a web application that allows to establish a video call with the model, having the unique number provided.
- During the photoshoot, all the photos are uploaded to the cloud as a convenient and reliable place for a photographer to keep session materials for further processing and post-production

How is a mobile phone’s unique identifier generated?
This 9-digit identifier (we refer to it as Shutter ID) is generated by the cloud server, when the model opens the Shutter App for the first time. The ID is generated out of random numbers, not taking into consideration any phone or user-related information. Which means that the Shutter ID that the model shares with the photographer can not allow anyone to identify the model in any way.
The fact is, thanks to Apple and Google security measures, when the model uninstalls the application and installs it again some time later, on the same phone or a different one – the server will generate a completely different identifier and will not be able to relate it to the previous one.
How can a model control who and when is allowed to connect to his/her phone and camera?
When we explain to photographers the benefits of using Shutter Studio for online photoshoots, we tend to describe it as “you get full control of the phone’s camera”. While this is technically true and taking over the camera allows the application to take photos with the best possible quality, that is not related to privacy at all.
First of all, built-in security mechanisms in iOS and Android do not allow an application to use the camera in background, only when the application is visible to a user and he or she is interacting with it.
Secondly, when the application tries to access a phone’s camera or microphone, it needs to ask for user’s permission first. And even more, at any moment in time, the user can navigate to phone’s settings and withdraw camera and microphone access permission.
And last but not least, from the model’s perspective, Shutter Studio can be considered as an improved video chat: in order to start the video session, the photographer needs to call the model first. And only after the model answers the incoming call, the application will turn on the camera and the microphone. And when the model hangs up for any reason, the call stops and no video or audio continues.
What about video sessions, can anyone else see or hear what is happening during the photoshoot?
All video sessions are established in a peer-to-peer way: the photographer connects directly to the model’s phone without any third-party involved. This is achieved by leveraging the famous WebRTC, originally developed by Google and now being an industry standard for audio and video communication over the Internet. Not only the peer-to-peer connection eliminates any clouds or servers in the middle, the whole video session is encrypted end-to-end, so that only the photographer and the model are capable of seeing the video. If any other person manages to silently intercept the communication, what he will get will be just random useless bits of data.
If you are ever interested in learning more details, here is a very interesting (but also pretty technical!) explanation how the technology works: https://webrtc-security.github.io/
How secure are photos uploaded to the Shutter Studio cloud?
As mentioned above, all the information that the model and the photographer exchange, is encrypted and secured in transit. For data protection at rest (i.e., after session materials has been uploaded to the Shutter Studio cloud during the photo sessions), we already implemented the following:
- Our servers are operated by well-known and well-trusted hosting providers, physically located in Europe
- The servers themselves are protected not only by hosting provider’s security infrastructure, but also by additional network and application firewalls, including secure private tunnels, to prevent malicious attackers from accessing data inside our servers or intercepting it during regular operation
- And of course, we provide a functionality to delete any individual photo or the whole photo shoot from the server, in a click of a button! This is very handy when you or your model are really not comfortable with knowing that some of your photos are backed up to the cloud
What’s next?
We are really excited with what we managed to achieve up to this point, especially given the current size of our team (which is – tiny! Just a couple of very enthusiastic and energized people!)
The safety measures in place are already a solid foundation for the majority of our users, Shutter Studio is now gaining popularity to shoot branding and content materials for small brands and businesses. With business starting to trust our solution, this really raises the bar, not only in overall reliability, but also in security and privacy.
Over the next few months, we will be dedicating ourselves to bringing your photos security to the next level. This will take a while, but we will approach this in small increments, so that every couple of weeks we become a bit better.
To start with, in early February, we will be releasing the first improvement to the Platform (web application for photographers and iOS and Android applications for models): all content that hits our servers will be stored encrypted. What does that mean?
- When a photo shoot happens, a new dedicated password (encryption key) will be generated, for this specific photo shoot only
- Every photo taken, when it is uploaded to the server, will be encrypted using this very password
- When the photographer or the model needs to review the photo, before it is sent to the phone or photographers computer, it will have to be decrypted first
- All encryption keys will be securely stored on a different hardware, specialised key vault, as we call it – very hard to break into
What are the benefits of the described solution? In an unlikely event of a security breach, if a malicious attacker gets access to our servers with photo session materials, he or she will not be able to use it – it will all be random unshaped bits of data. And given the number crunching power of modern computers, it will take literally several years to decrypt anything.
And for those who want more than that, with one more update we will implement a way for photographers to use their own passwords instead of automatically generated ones – so that no encryption keys will ever leave their personal devices, providing an ultimate level of data protection.
Thank you for reading this and being with us! We will post an update when we release the first update!